The way we secure our internet data is broken – or fairly close to being broken. Our curtain of confidentiality will soon be ripped away by new, powerful computing technology. Fortunately, there’s other technology that’s coming along that, some say, will help us protect communications even more securely than before.
Confusingly, there’s a single word attached to both the new method of attack and the new method of protection: quantum. Both attack and defence are rooted in quantum physics – but, I promise, we’ll leave the science alone.
Why is it important? Let’s start with a question. If you have data that’s stored in your systems and – because it always is these days – transmitted over fibre to other locations, how difficult for you would it be if it were released to a competitor, or a customer, or a lawyer, or a government? Not necessarily now but in, say, 2027, or 2032?
That could be your company’s financial information; or the medical records you are storing for a hospital; or designs for a new system – everything from a new car to a missile. How about your customers’ private data? Or your employees’ private data? Your emails? Your browsing habits? You bank account information and your travel history?
Some of this might be embarrassing if it were to be released or leaked. Some might be expensive or confidence-wrecking. Some might be career-ending.
In this feature I’m writing about why public-key cryptography (PKC) is at the end of its life after a remarkable 40 years or so. Of course, the industry hasn’t been using PKC for 40 years – mainly because it’s only in the past 20 years that we have been buying things on the internet, and therefore have wanted to keep our account information secret as it whizzed across the network.
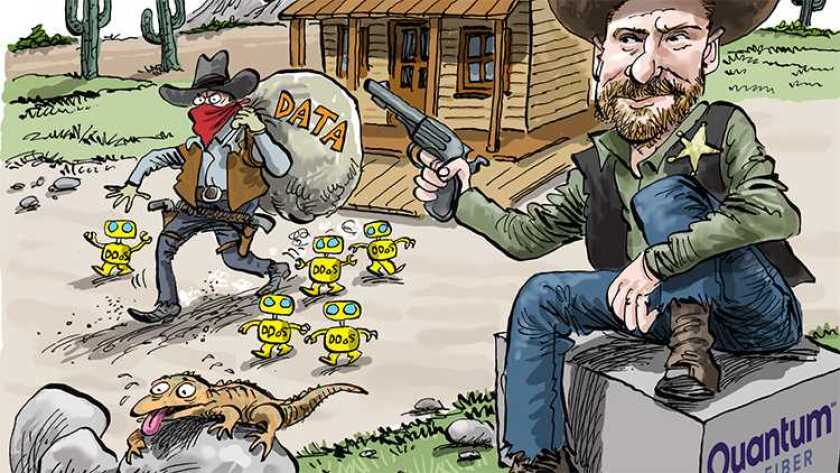
But the security of cryptography is about to be compromised by the arrival of new quantum-based computing techniques. At the same time new quantum-based cryptography techniques are coming, like the US Cavalry riding to the rescue of the Wells Fargo stagecoach, full of money, that’s about to be attacked by bandits.
Where the data is
A dumb reporter once asked a bank robber, Willie Sutton, why he robbed banks. “Because that’s where the money is,” he is alleged to have said, though later in life he denied that. Not the well-protected stagecoaches, you note: the banks.
In the same way, if you want to steal someone’s data, go for the nodes rather than the quantum-protected fibre links: that’s where the data is, as Sutton might have said.
Some say that quantum key cryptography (QKC) is the answer. Others say QKC is already broken and will be supplanted by post-quantum algorithms (PQA). Yet others say, nope, that’s no good either and here, out of the bag of tricks, is yet another quantum-related suggestion.
It’s clear, though, that cryptography as it is used in data communications today is nearing the end of its life. We are either going to go back to writing things on the back of postcards or we are going to have to find a better way.
Normally when anyone decides to write about quantum science or technology, they start by talking about Albert Einstein, Erwin Schrödinger – the cat man – and Werner Heisenberg. I’ve done it myself. I’ve quoted Einstein’s reputed comment that quantum science is “spooky action at a distance” and his question: “Does God play dice?”
And then we all go off to write about strangeness, and duality, and all the other things that are associated with quantummery. (I made that word up, by the way; if it’s in the OED or Webster’s Dictionary in 20 years, blame me.)
But I and my colleagues on Capacity, when we write about data centres, optical fibres and 5G, don’t discuss how transistors work in integrated circuits, how the refractive index of glass confines light to fibre, or Maxwell’s laws of electromagnetism. That’s because we are not talking about how it works, but what it all means and how it affects you in the industry. And this is what I want to do about quantum technology.
All this quantum science is leading to a technology that will arrive in your networks and data centres within a few years – five, maybe, or 10 or 15. That’s OK, you say. Plenty of time for the CTO to worry about it – or the CTO’s successor.
Misrouted data
But your data is already being compromised. It’s being misrouted over the internet, through apparently sporadic errors in border gateway protocol (BGP), the rules that allow the systems that make up the internet to send your information in the right direction.
There have been a few instances in the past few years where, for some inexplicable reason, traffic has gone off in a weird direction. It always ended up where it was supposed to be heading, but the idea is around that someone was intercepting the information, copying it and squirrelling it away, for the day when quantum computers would allow them to decode and read it.
Who says so? For a start, listen to Laura Thomas, a former CIA case officer who was the agency’s chief of base in Afghanistan. (Search online for her extraordinarily moving piece in The Cipher Brief on the West’s disastrous record in Afghanistan in 2020-21. Don’t bother looking at LinkedIn for her career history, though: her first job listed was in March 2021.)
Thomas, who is now senior director of national security solutions at Dan Caruso’s company, ColdQuanta, says these are “BGP hacks” and warns: “We know countries are harvesting data – it’s called harvest now, decrypt later. There’s a lot they can do. It’s like gold.”
Others in the industry agree. There are carriers – you’ve met them, I’ve met them – that are implicated in diverting traffic through nodes in places that are, shall we say, unfriendly to the West.
So, let’s look at quantum computing, and what it promises, and what it threatens. And then go on to ways of protecting data against the new threat – new data at least.
Andersen Cheng is CEO of a small cybersecurity company called Post-Quantum. He used to be with JP Morgan and then with the Carlyle Group, the private equity investor. He got involved in crypto in 2003 when he joined TRL Technology, which sells cyber security and counter terrorism solutions to governments.
Why is current cryptography under threat, I asked him. “A classical computer does serial computations, but very fast. There are many things a quantum machine can do, but it is useless at doing that. It is extremely powerful in doing the same thing over and over, a million times – and again and again.”
Prime numbers
Why is that important? At the heart of current cryptography is the multiplication of two prime numbers to produce a larger number. And then its factorisation back into the two primes.
Easy for short numbers, “but there are hundreds of numbers that it takes years to factorise,” Cheng tells me. In order to encrypt your data – for a bid on eBay or a supermarket purchase, or an ordinary email – the system uses long prime numbers. Conventional computers will crunch away for years: too long to be worthwhile. What you need is an answer in minutes or seconds.
Quantum computers that will do it in a short time “are becoming more available”, says Duncan Jones, head of quantum cyber security at Cambridge Quantum, a company that is in the process of merging with the quantum division of Honeywell. Cloud-based quantum computing services will be on the market in 2022, and that will mean that “people can genuinely experiment”, Jones says.
Like the CIA, which ColdQuanta’s Thomas used to work for, the UK’s National Cyber Security Centre (NCSC) has been aware of the threat for some time. The centre updated its white paper, Preparing for Quantum-Safe Cryptography, in November 2020. The “mathematical problems [of decoding encrypted information] would be easy to solve on a large, general-purpose quantum computer”, says NCSC, which is part of Government Communications Headquarters, one of the UK’s three main intelligence agencies.
So be warned. Current cryptography is obsolescent, if not already obsolete. What do you do to protect future data communications against the predations of quantum computing?
Quantum hype cycle
Here, the honest answer is: We don’t yet know. Or we can’t yet be sure. We are in the early phase of the quantum hype cycle, and different people are proposing different possible solutions.
Quantum-safe communications relies on the transmission of individual quantums of light to carry the keys that are used to encrypt the main data traffic. And, if the stream of quantums is intercepted, the quantums don’t get through – a quantum is either there or it isn’t. If it isn’t, you know there’s a problem, you know your signal is compromised, so you ignore that bit of the message. Quantum people talk happily of sending a new encryption key via QKD every few seconds.
Andrew Lord, senior manager of optical research at BT’s laboratories, and his team are working closely with Toshiba to try QKD in real-life communications. He’s running two trials, including one connecting London’s two main financial centres, the City, as it’s called, and Canary Wharf, just to the east.
“We are asking: ‘How do you use a [quantum] network? What would customers use this for?’,” he says. The idea is to test how quantum-secure networks will be used in real life – and to test their weak spots. “We have three exchanges that are clustered. The customer can go into one of these exchanges and come out of another. That’s harder to do in a secure way. You have to guarantee not getting keys to the wrong person.”
This is being run as part of BT’s regular business network, he says, installed by the company’s regular technical staff. “We are selling this properly as a BT-wide trial.”
No regeneration
The team has already identified some challenges – though BT is not alone in this. The biggest problem is that the quantums can’t travel far down a fibre – they are, after all, individual pulses of light, and you can’t even think about regenerating them, as that just replaces those quantums with others, losing the security in the process.
In June 2021, Andrew Shields, head of the quantum technology division at Toshiba Europe, reported that the company was able to transmit quantums securely as far as 600km, way more than the previous 100-200km limit.
Some are blunt to the point of cruelty. QKD is broken, they say. Even before it has started.
David Williams, founder and CEO of Arqit Quantum, wants to take it all into space. The company, having existed in stealth mode for years, did a reverse takeover by a Nasdaq-listed special-purpose vehicle, Centricus, in September 2021 that valued it at $1.4 billion. Now its market cap is $2.7 billion.
Arqit has “a lovely warm relationship with BT”, which has a global deal to market its services. These will use satellites to generate and deliver true random numbers that are quantum-generated. (Among the many issues with encryption techniques is that what purport to be random numbers, essential for maximum security, aren’t really random at all.)
Williams believes that not only is today’s public-key cryptography broken, after it has served us for decades, but that so is the post-quantum alternative. “Eventually a clever mathematician will find how to break it,” he warns.
But this is just as security is going to become rapidly more important, protecting data used for autonomous vehicles, the internet of things (IoT) and other services. “I will never put my family in an autonomous car unless it has Arqit kit,” says Williams.
Satellites to data centres
He notes also that post-quantum techniques create a huge computing load, and “for small IoT sensors that simply doesn’t work”, says Williams. “The great thing is that all of the heavy lifting is done by these satellites sharing quantum information down to data centres.”
Arqit says it has solved that problem by using its future satellites to generate truly random numbers.
So, where does this leave us? Ian West, head of the UK technology, media and telecoms practice in KPMG thinks that too many companies are leaving it too late.
“I try to explain to clients that quantum has potentially serious consequences. A really small proportion of clients are setting up quantum teams. Many are saying: ‘Worry about it tomorrow.’ Outside telecoms, the best I got was: ‘Yes, the CTO has heard of that.’ But that’s not enough.”
It’s important that organisations set up teams of people to investigate the quantum threat and opportunities – “teams that are accountable,” he says.
“And, don’t make it someone’s Saturday job. There is a wonderful opportunity but there is a threat as well,” West adds.
The last word should go to ColdQuanta’s Thomas, relatively recently out of Afghanistan.
“There is not a single bullet,” she says. “Post-quantum and QKD are waypoints. As long as human beings exist there will be vulnerabilities. I’m very wary of anyone who promises a 100% secure network.”
But the arrival of quantum, she says, is a technology that represents a platform shift. It’s comparable with the arrival of the steam engine, electricity and the internet. “Quantum is going to be very similar, when you look back on it.”